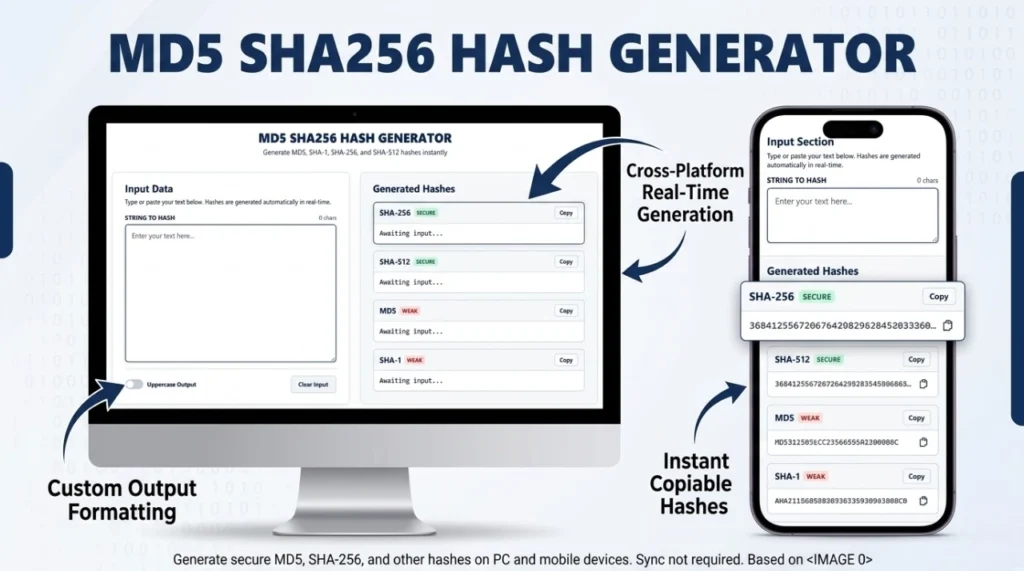
MD5 SHA256 HASH GENERATOR
Generate MD5, SHA-1, SHA-256, and SHA-512 hashes instantly
Input Data
Type or paste your text below. Hashes are generated automatically in real-time.
Generated Hashes
What is a md5 sha256 hash generator?
An online MD5 and SHA256 hash generator is a developer tool that converts variable-length input data (like a password, a sentence, or a file) into a fixed-length string of characters. This output is known as a hash, digest, or checksum. Cryptographic hash functions are deterministic—meaning the exact same input will always produce the exact same output hash, but even the slightest change to the input will drastically alter the entire hash.
Generate MD5 and SHA256 hashes instantly with our free online hash generator. Fast, secure tool for password hashing and data encryption.
How Does Our Online Hash Generator Work?
Our tool utilizes the widely trusted CryptoJS library to perform complex mathematical hashing algorithms entirely within your web browser. When you type into the input box, the tool simultaneously computes the mathematical digests for MD5, SHA-1, SHA-256, and SHA-512 in real-time.
Privacy Guarantee: Because this is a 100% client-side tool, your input text is never transmitted over the internet or saved to any external servers.
MD5 vs. SHA-256: Understanding the Differences
While both MD5 and SHA-256 are hashing algorithms, they serve very different purposes in modern computer science due to advancements in computing power.
| Feature | MD5 (Message Digest 5) | SHA-256 (Secure Hash Algorithm 2) |
|---|---|---|
| Hash Length | 128-bit (32 Hex Characters) | 256-bit (64 Hex Characters) |
| Security Status | Cryptographically Broken | Highly Secure |
| Processing Speed | Extremely Fast | Slightly Slower (More complex) |
| Primary Use Case | File checksums, non-secure data integrity checks. | SSL Certificates, Blockchain, Digital Signatures, secure integrity. |
Why You Should Never Use MD5 or SHA-1 for Passwords
Because MD5 and SHA-1 were designed to be fast, they are incredibly vulnerable to brute-force attacks. Modern graphics cards (GPUs) can compute billions of MD5 hashes per second. If you use an MD5 hash generator to store user passwords, hackers can crack your database in minutes using Rainbow Tables.
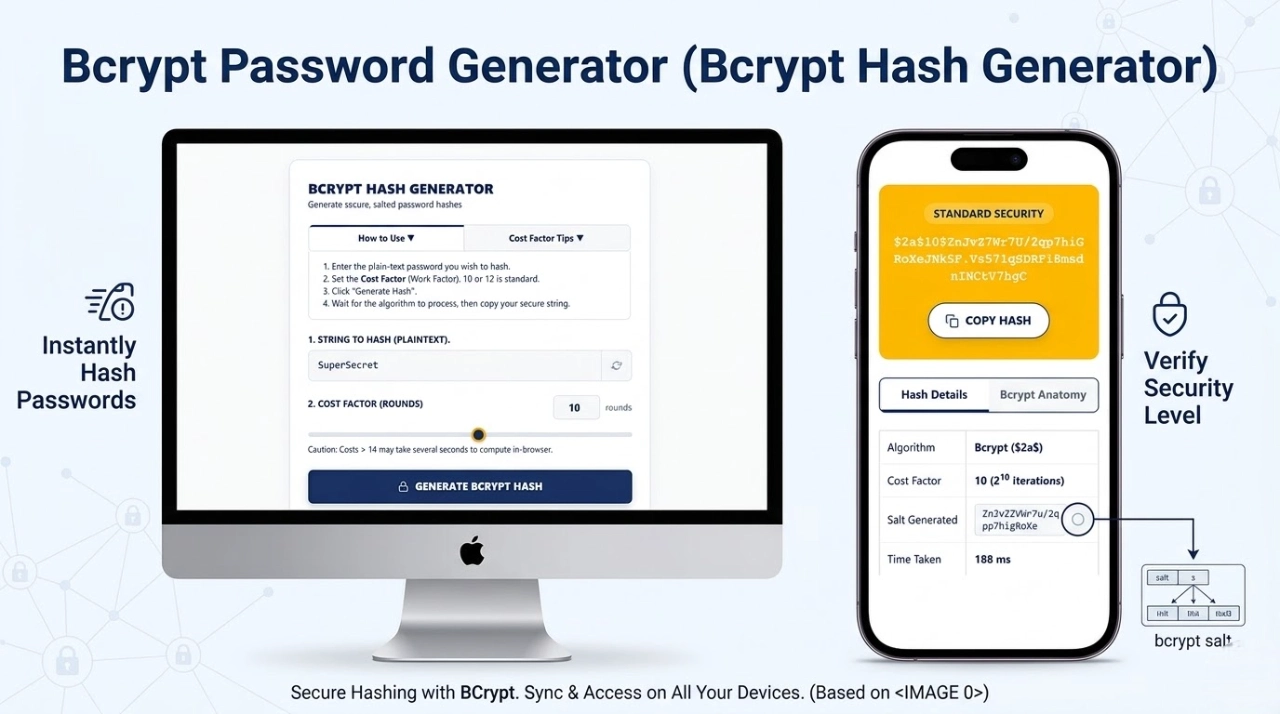
For secure password storage, you should never use standard fast hashes. Instead, use a slow, salted algorithm like Bcrypt. You can use our Bcrypt Password Generator for authenticating user credentials securely.
Common Use Cases for Hashing
- Verifying Data Integrity: When downloading a large software file (like an ISO image), the distributor often provides a SHA-256 checksum. You can hash the downloaded file on your machine and compare the hashes. If they match, the file downloaded perfectly without corruption.
- Digital Signatures: Hashing a document and then encrypting the hash with a private key ensures that a document hasn’t been tampered with in transit.
- Blockchain & Cryptocurrency: Bitcoin uses SHA-256 heavily to verify blocks of transactions through “Proof of Work.”
Understanding Hash Collisions
A “hash collision” occurs when two completely different pieces of input data accidentally produce the exact same output hash. Because MD5 only produces a 128-bit hash, the mathematical “pigeonhole principle” dictates that collisions are inevitable. In fact, researchers have publicly demonstrated how to intentionally create two different files that have the exact same MD5 hash.
This is why MD5 is considered “cryptographically broken.” SHA-256, producing a massive 256-bit space, has 2256 possible combinations. The chances of a SHA-256 collision are so infinitesimally small that it is currently considered impossible to force a collision with modern or even near-future computing power.
Frequently Asked Questions (FAQs)
Can I decrypt an MD5 or SHA-256 hash?
No. Hashing algorithms are one-way cryptographic functions. It is mathematically impossible to reverse-engineer the hash back into the original plaintext text. However, weak MD5 hashes can easily be “cracked” by comparing them against massive databases of pre-computed hashes.
What does SHA stand for?
SHA stands for Secure Hash Algorithm. It is a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S. Federal Information Processing Standard (FIPS).
Is SHA-512 better than SHA-256?
SHA-512 produces a longer, 512-bit hash, providing an even larger mathematical space against collisions. While technically more secure, SHA-256 is perfectly secure for almost all modern applications, including Bitcoin. Interestingly, on 64-bit processors, SHA-512 can actually compute faster than SHA-256 due to its underlying mathematical structure.